| 1. |
The Federal Information Security Management Act (FISMA) requires federal agencies to implement and support standardized IT security controls. These controls, defined by the National Institute of Standards and Technology (NIST), allow agencies to safely and confidently outsource critical applications to FISMA-compliant clouds, managed hosting environments and SaaS providers. Designed to Address Strict FISMA Standards More than half of all federal cabinet-level agencies — including Veterans Affairs, the De...
- Site Map
- Everyone: All Users
- 9/13/2017
- Relevance: 16
-
-
12/31/9999 11:59:59 PM
-
Fedramp, FISMA, Federal Government Hosting, 21st Century Digital Experience, Managed Services, FedRAMP Compliance, FISMA compliant, US Government
-
-
-
-
-
-
-
-
12/20/2023 3:53:17 PM
-
-
|
| 2. |
You need to evolve and innovate to be successful. But the cloud is as complex as it is powerful. Our staff and partnership with Rackspace leverages the right experts and environments who are certified in all the leading public cloud platforms and technologies — so you don’t have to be. Oxcyon, through it's partnership with Rackspace offers managed security services to help you leverage the public, private, hybrid and multi-cloud offerings while meeting even the most stringent security and compliance requ...
- Security Policies
- General
- Everyone: All Users
- 10/25/2022
- Relevance: 16
-
-
12/31/9999 11:59:59 PM
-
Centralpiont Hosting & Security Policies, Cloud, Host, Hosting, Compliance, Certificate, Centralpoint, Oxcyon, Gartner, Digital Experience, Knowledge Management, Data Mining, Document Retention, Data Aggregation, Inference Engine, Technical, Specifications, Stack, Content Management, Sharepoint Alternative, Big Data, Metadata, Automate metadata, Taxonomy, Enterprise, Magic Quadrant, Centralpoint Compliance, Centralpoint Technical
-
-
-
-
-
-
-
-
3/27/2023 4:02:27 PM
-
-
|
| 3. |
- Centralpoint Module Gallery
- Deep Dive - Video Overview
- Everyone: All Users
- 3/28/2019
- Relevance: 11
-
-
12/31/9999 11:59:59 PM
-
Retention Policies, Document Retention Policies, Automate Retention Policies, Schedule Retention, Document Deletion, Archiving Documents, metadata,ontology,intranet,portal,transformation,Artificial Intelligence,aggregation
-
Automate document retention policies using Centralpoint. It equips you with user-friendly tools for defining diverse retention policies, incorporating custom filters, queries, and start/end dates. Centralpoint also manages storage repository data, connecting to File Folders, SQL, Oracle, IBM, and third-party providers like Workday, Citibank, and ADP.
Centralpoint's scheduled feature regularly scans these repositories, as per your chosen frequency, to identify expired records per your policies. Detected files can be routed to administrators for approval of destruction. Upon approval, Centralpoint systematically eradicates records from each system, meticulously recording each step. With Centralpoint's automated document retention policy management, ongoing compliance is effortlessly maintained.
Businesses are required by law to retain confidential client, employee, and company information for a minimal amount of time. But many documents eventually outlive their purpose, and holding onto them for too long puts you at risk of a security breach and non-compliance with today’s privacy legislation. How long you store business records should be determined by a retention schedule that balances each record’s usefulness with the legal requirements. This schedule will depend on the type of business and the lifecycle of specific documents.
Below is a document retention schedule that outlines how long you should hold on to important documents. After their retention period is complete, you should ensure that they are securely destroyed by a third-party information security provider. Please note that these recommendations on document retention are general guidelines only. They are not intended to represent legal advice. Contact your legal expert(s) or federal, state or provincial government to ensure you are following current legal requirements for your area.
Alphabetized by Document Category
| ACCOUNTING |
Retention Period |
| AR/AP Ledger |
7 Years |
| Bank Reconciliations |
2 Years |
| Cash Disbursements/ Receipts |
Permanently |
| Chart of Accounts |
Permanently |
| Depreciation Schedule |
Permanently |
| Expense Reports |
7 years |
| Financial Statements |
Permanently |
| General Ledger |
Permanently |
| Inventory Records |
Permanently |
| Journal Entries |
Permanently |
| Petty Cash Records |
7 years |
| Tax Returns |
Permanently |
| HUMAN RESOURCES & PAYROLL |
Retention Period |
| Accident Reports |
7 Years |
| Attendance |
7 Years |
| Benefits |
5-7 Years |
| Employment Applications |
3 Years |
| Payroll - After Termination |
10 Years |
| Personnel - After Termination |
7 Years |
| Personnel - Current Employee |
Permanently |
| Safety Reports |
5 Years |
| Salary History |
8 Years |
| Time Reports |
7 Years |
| SHIPPING AND RECEIVING |
Retention Period |
| Export Declarations |
4 Years |
| Freight Bills |
4 Years |
| Manifests |
4 Years |
| Waybills and Bills of Lading |
4 Years |
| CORPORATE / LEGAL |
Retention Period |
| Annual Report |
Permanently |
| Articles of Incorporation |
Permanently |
| Audit Reports - External |
Permanently |
| Audit Reports - Internal |
6 Years |
| Contracts |
Permanently |
| Copyrights, Trademarks, Patents |
Permanently |
| Correspondence, General |
2 Years |
| Correspondence, Legal/Tax |
Permanently |
| Correspondence, Routine |
7 Years |
| Mortgages, Licences, Deeds |
Permanently |
| Organizational Charts |
Permanently |
| Partnership Agreements |
Permanently |
| PURCHASING AND SALES |
Retention Period |
| Purchase orders |
3 Years |
| Requisitions |
3 Years |
| Sales contracts |
3 Years |
| Sales invoices |
3 Years |
* Retention periods begin after the termination, expiration, disposal, etc., of the item.
-
-
-
-
-
-
-
2/19/2024 12:10:00 PM
-
https://qc.xoprod20.com/Uploads/Public/Blogs/DocumentRetentionCompliant3.gif
-
|
| 4. |
- Centralpoint Module Gallery
- Everyone: All Users
- 6/3/2021
- Relevance: 11
-
-
12/31/9999 11:59:59 PM
-
Office 365, o365, Azure Cloud, Cloud, Graph, metadata,ontology,intranet,portal,transformation,Artificial Intelligence,aggregation
-
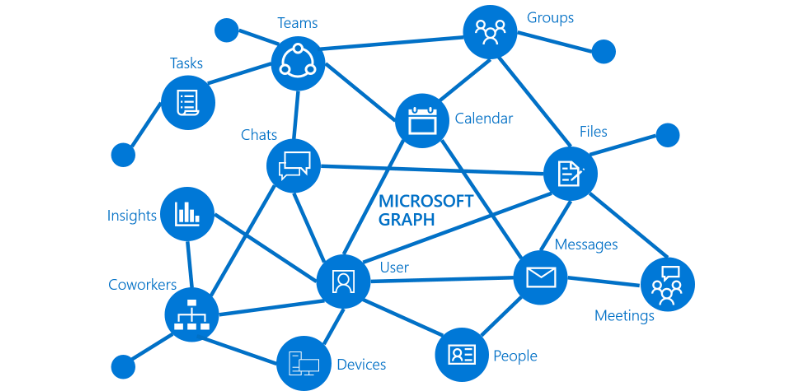
Centralpoint's Data Transfer utilities are integrated with Office 365, and Azure Cloud, via Microsoft Graph. This allows for records in o365 to be indexed, ingested, and receive automated metadata from o365. This data transfer routine requires the administrator Verify their identity before running, or scheduling to run periodically. For more information, please see Data Transfer, Data Transformation, Data Mining, and Automated Metadata. Please find below information on the Microsoft Graph Integration and how it works:
What is Microsoft Graph?
Microsoft Graph exposes REST APIs and client libraries to access data on the following Microsoft cloud services:
- Microsoft 365 core services: Bookings, Calendar, Delve, Excel, Microsoft 365 compliance eDiscovery, Microsoft Search, OneDrive, OneNote, Outlook/Exchange, People (Outlook contacts), Planner, SharePoint, Teams, To Do, Workplace Analytics.
- Enterprise Mobility and Security services: Advanced Threat Analytics, Advanced Threat Protection, Azure Active Directory, Identity Manager, and Intune.
- Windows 10 services: activities, devices, notifications, Universal Print.
- Dynamics 365 Business Central.
To find out more, see Major services and features in Microsoft Graph.
What can you do with Microsoft Graph?
Use Microsoft Graph to build experiences around the user's unique context to help them be more productive. Imagine an app that...
- Looks at your next meeting and helps you prepare for it by providing profile information for attendees, including their job titles and managers, as well as information about the latest documents they're working on, and people they're collaborating with.
- Scans your calendar, and suggests the best times for the next team meeting.
- Fetches the latest sales projection chart from an Excel file in your OneDrive and lets you update the forecast in real time, all from your phone.
- Subscribes to changes in your calendar, sends you an alert when you’re spending too much time in meetings, and provides recommendations for the ones you can miss or delegate based on how relevant the attendees are to you.
- Helps you sort out personal and work information on your phone; for example, by categorizing pictures that should go to your personal OneDrive and business receipts that should go to your OneDrive for Business.
- Analyzes at-scale Microsoft 365 data so that decision makers can unlock valuable insights into time allocation and collaboration patterns that improve business productivity.
- Brings custom business data into Microsoft Graph, indexing it to make it searchable along with data from Microsoft 365 services.
Pick the first scenario about researching meeting attendees as an example. With the Microsoft Graph API, you can:
- Get the email addresses of the meeting event attendees.
- Look them up individually as a user in Azure Active Directory to get their profile information.
You can then navigate to other resources using relationships:
Microsoft Graph continues to open up the Microsoft 365 platform for developers, and always only with the appropriate permissions
Popular API requests
Check out some of these common scenarios for working with the Microsoft Graph API. The links take you to the Graph Explorer.
Bring data from an external content source to Microsoft Graph (preview)
Use Microsoft Graph connectors to bring data that is external to the Microsoft cloud into Microsoft Graph. Examples of such data can be an organization's human resources database or product catalog, hosted on-premises or in the public or private clouds.
Microsoft Graph connectors create connections to external data sources, index the data, and store it as external custom items and files. Once indexed, those items can show up in Microsoft Search, and for apps that use the Microsoft Search API.
Access Microsoft Graph data at scale using Microsoft Graph Data Connect
Use Microsoft Graph Data Connect to access data on Microsoft Graph at scale, while allowing administrators granular consent and full control over their Microsoft Graph data. Data Connect streamlines the delivery of this data to Microsoft Azure.
Using Azure tools, you can then build intelligent apps that:
- Find you the closest expert on a topic to you in your organization
- Automate knowledge base creation
- Analyze meeting requests to provide insights into conference room utilization
- Detect fraud with productivity and communication data
When should I use Microsoft Graph API or Data Connect?
Microsoft Graph Data Connect provides a new way for you to interact with the data that's available through Microsoft Graph APIs. Data Connect provides a unique set of tools that streamline the building of intelligent applications, all within the Microsoft cloud.
-
-
-
-
-
-
-
2/19/2024 12:09:07 PM
-
https://qc.xoprod20.com/Uploads/Public/BG/microsoft-graph-dataconnect-connectors-enhance.png
-
|
| 5. |
Automate Document Retention Policy Mangagement with Centralpoint
- Site Map
- Everyone: All Users
- 3/28/2019
- Relevance: 11
-
-
12/31/9999 11:59:59 PM
-
Document Retention, Retention Policy Management, Retention Policies, Automated Document Retention, Scheduled Retention Policies, Automate Retention Management, Archives, Retention, On premise document retention
-
-
-
-
-
-
-
-
8/10/2023 4:49:13 PM
-
-
|
| 6. |
- Security Policies
- Security
- Everyone: All Users
- 7/14/2022
- Relevance: 11
-
-
12/31/9999 11:59:59 PM
-
-
-
-
-
-
-
-
-
3/27/2023 4:03:52 PM
-
-
|
| 7. |
What is Retention Policy Management, and why do you need a system to keep up with it? Document or Records Retention Management deals with the policies which your organization must follow, keeping some records on file for a certain period of time, and making sure that others are deleted and not on file, after that retention policy period. Here are samples of common document retention policies. These rules can change drastically based upon your industry type, and changing regulations. Do not use thes...
- Site Map
- Everyone: All Users
- 4/12/2019
- Relevance: 11
-
-
12/31/9999 11:59:59 PM
-
Records retention, Document Retention, Retention Policies, Retention Policy Management, Expired Documents, Archives, Automating deletion of documents
-
-
-
-
-
-
-
-
4/12/2019 8:39:25 AM
-
-
|
| 8. |
Businesses are required by law to retain confidential client, employee, and company information for a minimal amount of time. But many documents eventually outlive their purpose, and holding onto them for too long puts you at risk of a security breach and non-compliance with today’s privacy legislation. How long you store business records should be determined by a retention schedule that balances each record’s usefulness with the legal requirements. This schedule will depend on the type of business...
- Site Map
- Everyone: All Users
- 3/14/2019
- Relevance: 11
-
-
12/31/9999 11:59:59 PM
-
-
-
-
-
-
-
-
-
3/14/2019 9:35:25 AM
-
-
|
| 9. |
Oxcyon, is compliant with ISO27k by proxy of Certificate Number OHS 587454 . Those prefixed with ‘A’ are listed in Annex A of ISO/IEC 27001:2013 and are explained in more detail in ISO/IEC 27002:2013. Further ISO27k standards fill-in various supplementary details ( e.g. ISO/IEC 27005 on information risk management and ISO/IEC 27018 on privacy in cloud computing), while other ISO and non-ISO standards and resources provide lots more information, and in some cases recommend alternative o...
- Site Map
- Everyone: All Users
- 8/2/2014
- Relevance: 11
-
-
12/31/9999 11:59:59 PM
-
ISO27K, EU, EU Compliance, Standards, Policy, ISO/IEC 27001:2013
-
-
-
-
-
-
-
-
8/8/2017 11:24:16 AM
-
-
|